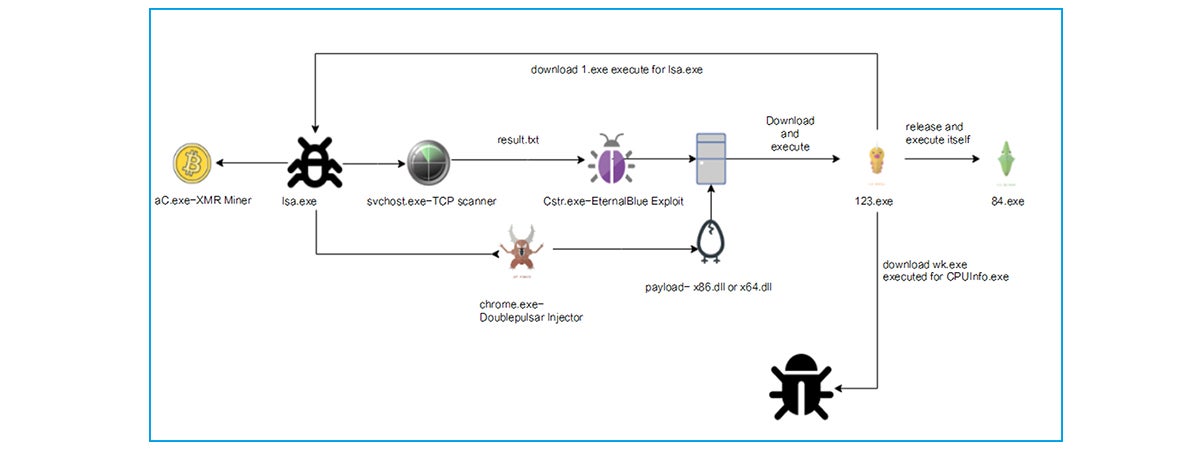
Recently, Sangfor Security Team discovered that a Trojan dubbed ZombieBoy has stealthily infected computers from various industries worldwide. This Trojan has multiple malicious modules including intranet scanner, EternalBlue vulnerability exploit, DoublePulsar backdoor and crypto-mining tool, featuring capabilities of spread, remote control and cryptocurrency mining. It is dubbed ZombieBoy because it exploits a tool named ZombieBoy when dropping the first malicious DLL file, and shares similar structure with MassMine.
It was first spotted at the end of 2017. In 2018, various security vendors released analysis on this Trojan and later security media reported that over 70,000 hosts were controlled by this Trojan. As of now, Sangfor Neural-X found that it spread quickly in a variety of industries, which include enterprise, education and government. Enterprises with weak security protection capabilities are infected the most.
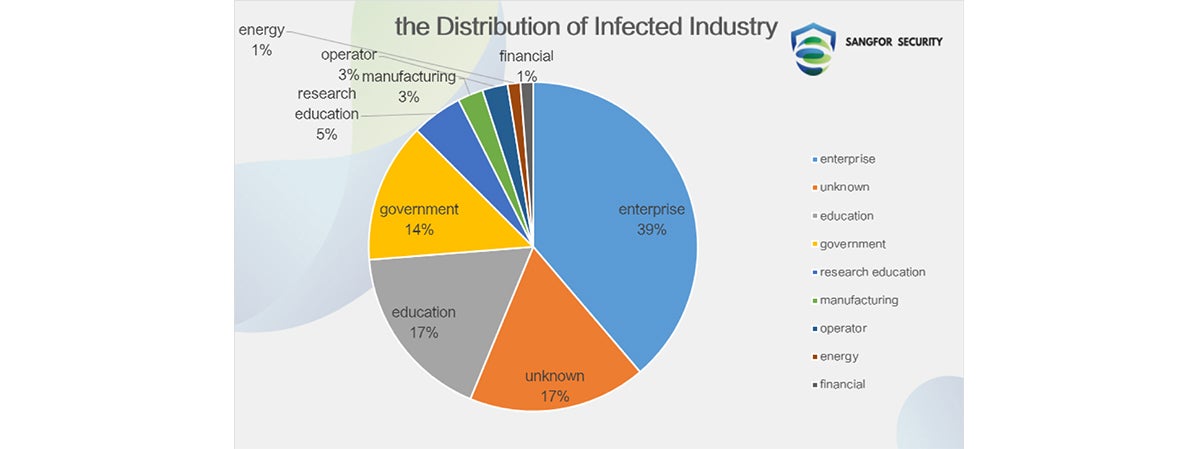
The analysis data by Sangfor Neural-X shows that the Trojan did not have specific targets and affected users from different countries.
Symptoms
An unknown policy appears in IP security Polices, which blocks access on the port 445 from any IP addresses except 22.148.18.88.
The IP address location lookup result shows that suspicious IP address belongs to US.

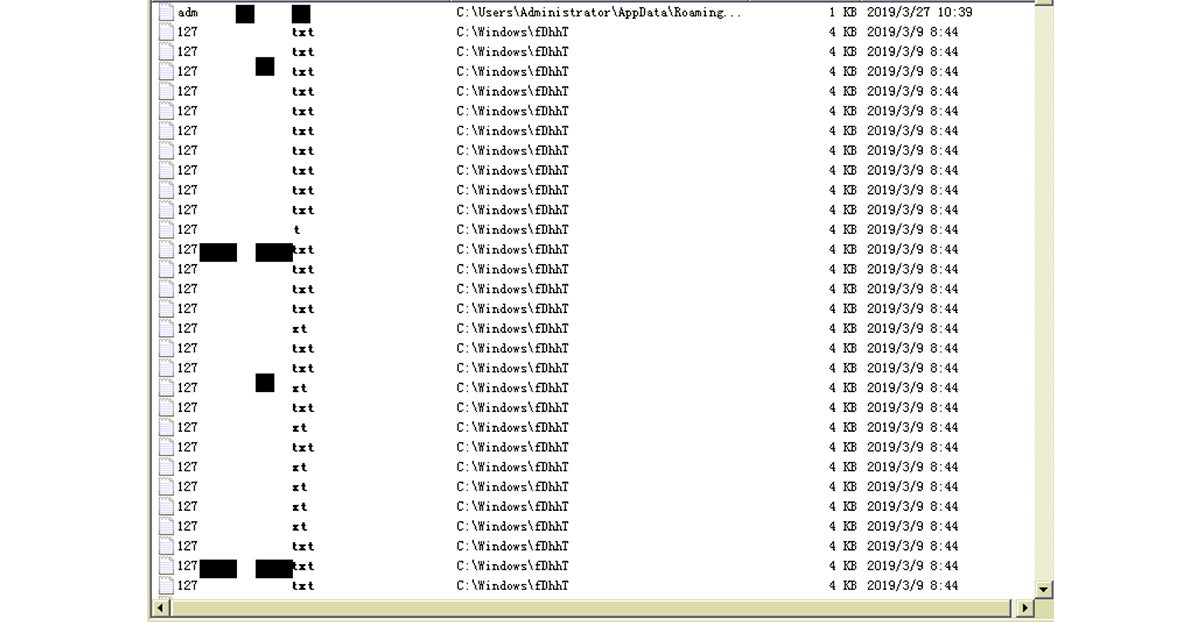
By searching for newly-created txt files, it shows massive IP.TXT files which are logs of the module used for spreading the Trojan in intranet.
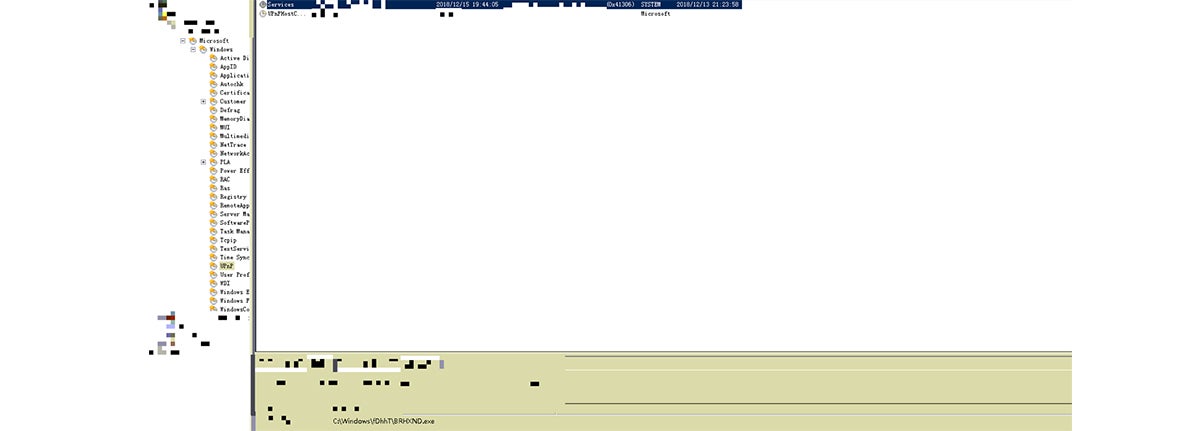
The figure below shows a task which executes a malicious file under Trojan directory.
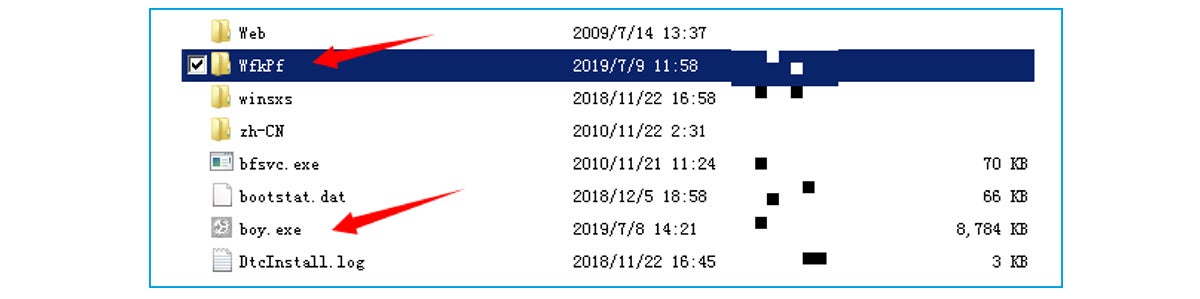
The virus vector creates a folder with a name of randomly chosen 5-digit letters in Windows directory and releases Trojan file boy.exe:
There is a malicious mining program running:
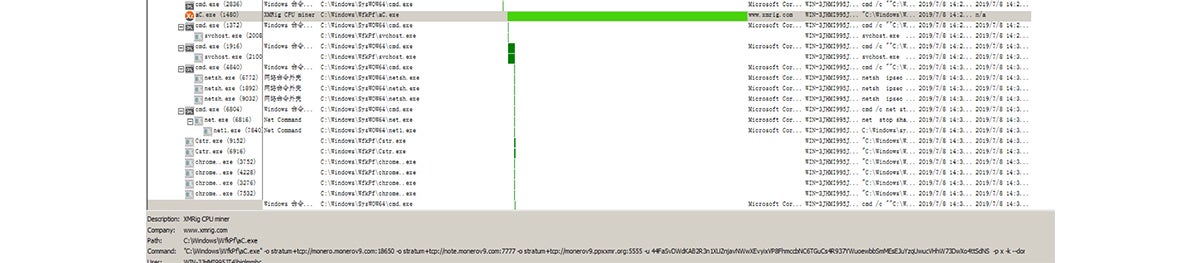
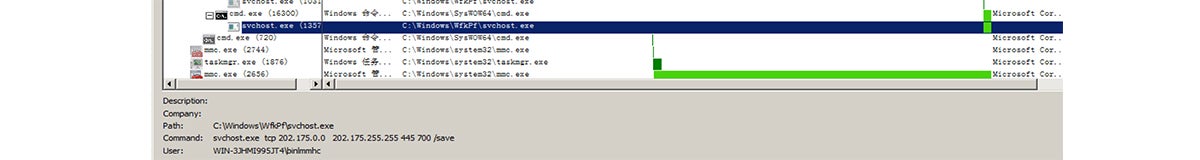
Process of an open-source scanner developed by WinEggDrop:
EternalBlue vulnerability exploit Cstrl.exe:
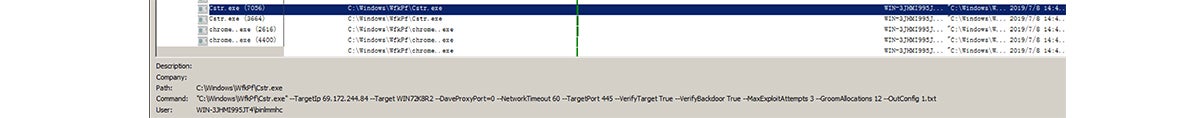
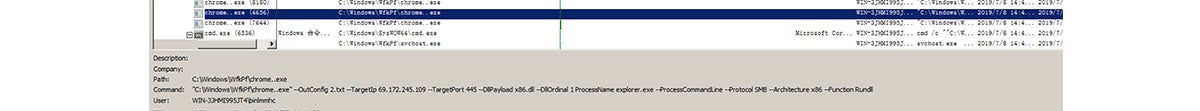
DoublePulsar backdoor implant chrome.exe:
Solution
1. Install MS17-010 patches to fix vulnerability.
2. Disable necessary ports, such as 135, 137, 138, 139, 445.
Sangfor EDR, NGAF and Security Intelligence products are capable of detecting this virus.
3. Deploy Sangfor security product and connect to cloud-based Sangfor Neural-X to detect new threats.
4. Sangfor offers customers and users free anti-malware software to scan for and remove the virus.
Indicators of Compromise (IOC):
URL:
http://ca.monerov9.com:443/123.exe
http://v9.monerov8.com:8800/A.TXT
http://103.246.218.247:443/1
http://103.246.218.189:8800/1
http://103.246.218.189:8800/wk.exe
http://wk.monerov9.com:443/wkgx.exe
DNS:
dns.fq520000.org
monero.monerov9.com:18650
note.monerov9.com:7777
monerov9.ppxxmr.org:5555
Wallet Address:
44FaSvDWdKAB2R3n1XUZnjavNWwXEvyixVP8FhmccbNC6TGuCs4R937YWuoewbbSmMEsEJuYzqUwucVHhW73DwXo4ttSdNS
MD5:
263584AF66662C6589D8D646E15965F7
78C317B9D69241405A3340E6821D7870
648C99C15575BA3E6237E01D7C235829
31D696F93EC84E635C4560034340E171
770D0CAA24D964EA7C04FF5DAF290F08
C24315B0585B852110977DACAFE6C8C1
EE2D6E1D976A3A92FB1C2524278922AE
A539D27F33EF16E52430D3D2E92E9D5C
3C2FE2DBDF09CFA869344FDB53307CB2
B713AF19C38A0B91ED6E72C8C64F843B
F82FA69BFE0522163EB0CF8365497DA2
8C80DD97C37525927C1E549CB59BCBF3
1CA9E6EB86036DAEA4DFA3297F70D542
A05C7011AB464E6C353A057973F5A06E
D9B5B26F0423230E99768092F17919A3
3E5D06DC6E7890E1800CF24C9F599856
4FF94C163565A38A27CF997AD07B3D69
1F0669F13DC0545917E8397063F806DB
47106682E18B0C53881252061FFCAA2D
24AA99837D14BEE5DA2E2339B07F9D4C
89B7DAC7D9CE5B75B08F5D037EDD3869
BA629216DB6CF7C0C720054B0C9A13F3
649B368C52DE83E52474A20CE4F83425
4803A7863DA607333378B773B6A17F4C
9026563DAB83DF2678253634760139ED
43AAC72A9602EF53C5769F04E1BE7386
F01F09FE90D0F810C44DCE4E94785227
5ADCBE8BBBA0F6E733550CE8A9762FA0
9A5CEC05E9C158CBC51CDC972693363D
6FE4544D00B77E0295E779E82D8F0FE5
00DD6B018C3C2D347DF43F779715BCA5
09836461312A3781AF6E1298C6B2C249
30017E300C6D92E126BF92017C195C37
2F0A52CE4F445C6E656ECEBBCACEADE5
B777086FD83D0BC1DCCDC7C126B207D0
8969668746AE64CA002CC7289CD1C5DA
E53F9E6F1916103AAB8703160AD130C0
5E8ECDC3E70E2ECB0893CBDA2C18906F
C097FD043D3CBABCADA0878505C7AFA5
0647DCD31C77D1EE6F8FAC285104771A
F0881D5A7F75389DEBA3EFF3F4DF09AC
F61E81EAF4A9AC9CD52010DA3954C2A9
8B0A4CE79F5ECDB17AD168E35DB0D0F9
838CEB02081AC27DE43DA56BEC20FC76
01D5ADBFEE39C5807EE46F7990F5FDA7
46F7B320B13A4B618946042360215179
3E89C56056E5525BF4D9E52B28FBBCA7
D1AAE806243CC0BEDB83A22919A3A660
83076104AE977D850D1E015704E5730A
1FA609BC0D252CA0915D6AED2DF7CCC2
6B7276E4AA7A1E50735D2F6923B40DE4
9814F6E092E45BDFE4C47C6A2DE5D31F
F180502593A00678E7F481B21BE1AA9A
5B72CCFA122E403919A613785779AF49
9744F0000284C2807DE0651C7E0D980A
E4AD4DF4E41240587B4FE8BBCB32DB15





